 Security
Security
Search Results
Results for "Spring Security"
110 articles found
 Security
Security
 Frameworks
Frameworks
Spring Boot vs. Micronaut: Which Framework Wins?
For the last five years, Spring Boot has been my default choice for microservices. It’s the Swiss Army knife of Java frameworks. But recently, I started…
 Web Development
Web Development
Building REST APIs with Spring Boot: A Practical Guide
Building a REST API used to involve a lot of XML configuration in the old J2EE days. Spring Boot changed all that with auto-configuration. I can now spin u…
 Advanced Java
Advanced Java
Using GraalVM for Native Images: Faster Startup, Lower Memory
The biggest criticism of Java in the serverless world has been startup time. A cold start of a Spring Boot app can take 20-30 seconds. GraalVM changes that…
 Security
Security
Content Security Policy (CSP): Hardening Web Applications
Content Security Policy (CSP) is one of the most effective security headers for preventing XSS attacks, yet it remains underutilized. CSP lets you define w…
 DevOps
DevOps
Containerizing Java Apps: Docker and Kubernetes
The days of deploying a WAR file to a Tomcat instance on a virtual machine are fading. Most Java shops are moving to containers. I started Dockerizing my S…
 Databases
Databases
The Repository Pattern with Spring Data JPA
When I first started using Spring Data JPA, I was amazed that I could just create an interface extending `JpaRepository` and get CRUD methods for free. But…
 Spring Framework
Spring Framework
Dependency Injection: Why `new` Is Not Always Your Friend
Early in my career, I used the `new` keyword everywhere. `new UserService(new UserRepository(new Database()))`. I thought I was being efficient. Then came…
 Cybersecurity
Cybersecurity
Cybersecurity: Protecting the Digital World
I was a history major, which seems like a weird path to cybersecurity. But I was always into puzzles and logic. After taking a few online courses, I got my…
 Technology
Technology
The Role of AI in Cybersecurity: Staying Safe in a Digital World
As cyber threats become more sophisticated, our defenses must evolve. AI has become an indispensable tool in the fight against cybercrime, acting as a tire…
 How to Use Claude
How to Use Claude
Claude in the Enterprise: Deployment, Security, and Governance
Enterprise adoption of Claude is growing fast, but enterprise deployments have requirements that consumer use doesn't — security, compliance, governance…
 Security
Security
Web Security Fundamentals: Protecting Your Site from Common Attacks
Security isn't something you add after building a site—it needs to be baked into your development process. Cross-Site Scripting (XSS) remains one of the…
 Java Fundamentals
Java Fundamentals
Why Java Still Dominates Enterprise Development in 2024
I’ve been a full-stack developer for about a decade now, and if there’s one language I keep coming back to, it’s Java. It’s not the flashiest, and…
 Reactive Programming
Reactive Programming
Introduction to Reactive Programming with Project Reactor
Asynchronous programming used to give me headaches until I started using Project Reactor. It’s the foundation of Spring WebFlux, and it changes how you t…
 Destinations
Destinations
The Best Time of Year to Visit Florida (It’s Not Summer)
Everyone thinks of Florida in July, but that’s a mistake unless you like saunas. I went to Orlando in August once and the humidity was so thick you could…
 Animation
Animation
Motion Design on the Web: Framer Motion and Advanced Animation
Motion design elevates web experiences from functional to delightful. Framer Motion has become the standard for React animations, providing a declarative A…
 Rise of America
Rise of America
The Marshall Plan: How America Built the World It Wanted to Live In
In June 1947, Secretary of State George Marshall gave a commencement address at Harvard that would change the postwar world. He proposed that the United St…
 Security
Security
WebAuthn: Passwordless Authentication with Biometrics
WebAuthn (Web Authentication) is a browser API that enables passwordless authentication using biometrics (fingerprint, face ID), security keys (YubiKey), o…
 Rise of America
Rise of America
America After 9/11: Power and Its Limits
On the morning of September 11, 2001, the most powerful country in the world — the sole superpower of the unipolar moment, the country that had just won…
 Regional Security
Regional Security
The Rise of the Taliban: India’s Afghan Conundrum
For two decades, India invested heavily in Afghanistan—building the Parliament, roads, dams. We had a strategic partnership with the old government. Then…
 Rise of America
Rise of America
The New Deal: When America Reinvented Its Government
By March 4, 1933, the day Franklin Delano Roosevelt was inaugurated as the thirty-second president of the United States, the American economy was in a stat…
 Security
Security
The Dark Side of AI Agents: Security Risks You Need to Know
Okay, let’s be real for a minute. Handing over your passwords and API keys to an autonomous piece of software is a security nightmare waiting to happen i…
 Lifestyle
Lifestyle
The AI-Powered Home: Making Life Easier with Smart Tech
The smart home is no longer a futuristic fantasy; it's a reality, and AI is its brain. The goal of an AI-powered home is not just to have gadgets, but to c…
 Software
Software
Microsoft's Windows 11 Demands Are Leaving Millions of Computers Behind
Windows 11 requires TPM 2.0. That is a security chip. Most computers from before 2018 do not have it. Microsoft says it is for your safety. Critics say it…
 Career
Career
Java Career Advice: What I Wish I Knew as a Junior
If I could go back and give myself advice, I’d say: don’t just learn the syntax. Learn the ecosystem. Knowing Java is great, but knowing Spring, Maven…
 Advanced Java
Advanced Java
Understanding Java Annotations and Annotation Processing
Annotations in Java are like magic markers. They started as just metadata (`@Override`), but with frameworks like Spring and Lombok, they have become power…
 Databases
Databases
Database Access with JPA and Hibernate
When I first learned SQL, I loved it. But mapping SQL results to Java objects manually with JDBC is tedious. That’s where JPA (Java Persistence API) and…
 Dating
Dating
Best Dating Places in America: Portland Japanese Garden
The Portland Japanese Garden is often considered one of the most authentic Japanese gardens outside of Japan, and it is an incredibly serene setting for a…
 Romance
Romance
Heartstopper Season 4: The Beloved LGBTQ+ Romance Continues
Heartstopper has become one of Netflix's most heartwarming and important series, adapting Alice Oseman's beloved graphic novels with tenderness and authent…
 Dating
Dating
Best Dating Places in America: Miami South Beach Boardwalk
Miami’s South Beach boardwalk is one of those places that works for any kind of date. You can keep it casual with a walk during the day, watching the col…
 Dating
Dating
Best Dating Places in America: Portland Japanese Garden
The Portland Japanese Garden is often considered one of the most authentic Japanese gardens outside of Japan, and it is an incredibly serene setting for a…
 Dating
Dating
Best Dating Places in America: Miami South Beach Boardwalk
Miami’s South Beach boardwalk is one of those places that works for any kind of date. You can keep it casual with a walk during the day, watching the col…
 Healthcare
Healthcare
The Town in Texas That Lost Its Only Hospital – And What Happened Next
Down in rural West Texas, there's a small town called Crane. Population just over 4,000. Last spring, their only hospital shut its doors. You'd think that…
 Dating
Dating
Best Dating Places in America: Miami South Beach Boardwalk
Miami’s South Beach boardwalk is one of those places that works for any kind of date. You can keep it casual with a walk during the day, watching the col…
 Dating
Dating
Best Dating Places in America: Portland Japanese Garden
The Portland Japanese Garden is often considered one of the most authentic Japanese gardens outside of Japan, and it is an incredibly serene setting for a…
 Politics
Politics
I Volunteered for a Campaign for One Weekend. Here's What Shocked Me.
My friend dragged me to a state senate campaign office last spring. I expected suits and speeches. Instead, I got a folding table, a tattered list of phone…
 Energy Politics
Energy Politics
Energy Security: Why India is Hugging Russia and Irking the US
Energy is the currency of geopolitics. When Russia invaded Ukraine, the West expected India to jump on the sanctions bandwagon. Instead, we did the opposit…
 Technology
Technology
The Future of Remote Work: Tools and Tech Shaping Collaboration
Remote work is here to stay, and the technology supporting it is evolving beyond simple video conferencing. The future of work is hybrid, requiring seamles…
 Jobs
Jobs
How to Get a UAE Golden Visa: The Complete 2025 Guide
The UAE's Golden Visa programme, launched in 2019 and significantly expanded since, offers 10-year residency to a broad range of eligible individuals witho…
 Google Cloud Platform
Google Cloud Platform
Secrets Manager: Where I Finally Stopped Hardcoding API Keys
We've all done it. Hardcoded API keys in config files. Committed them to Git. Then scrambled to revoke them when you realize the repo is public. I was guil…
 Google Cloud Platform
Google Cloud Platform
Artifact Registry: Where My Containers Go to Be Safe
I used Docker Hub for a while. It was fine until I had a private image that I didn't want public. Then I discovered Artifact Registry on GCP. It's a privat…
 How to Use Claude
How to Use Claude
How Claude Reads and Analyzes Code: A Developer's View
Beyond writing code, Claude is remarkably capable at understanding and analyzing existing codebases. For developers working in complex systems, this analys…
 Air Travel
Air Travel
Navigating Airport Security Like a Pro
I used to be the person fumbling with my shoes, holding up the line. Now, I’ve got it down to a science. Wear slip-on shoes. Have your liquids in a clear…
 Google Cloud Platform
Google Cloud Platform
Secrets Manager: Where I Finally Stopped Hardcoding API Keys
We've all done it. Hardcoded API keys in config files. Committed them to Git. Then scrambled to revoke them when you realize the repo is public. I was guil…
 Google Cloud Platform
Google Cloud Platform
Artifact Registry: Where My Containers Go to Be Safe
I used Docker Hub for a while. It was fine until I had a private image that I didn't want public. Then I discovered Artifact Registry on GCP. It's a privat…
 AWS
AWS
AWS KMS: Managing Encryption Keys
Key Management Service lets you create and manage encryption keys. I use it to encrypt S3 buckets, EBS volumes, and RDS databases. KMS integrates with many…
 AWS
AWS
AWS Identity and Access Management: Who Gets In?
IAM is the security guard of AWS. It controls who can access what. The biggest mistake I see beginners make is using the root user for everything. The root…
 AWS
AWS
AWS WAF: Protecting Your Web Applications
AWS WAF is a web application firewall that helps protect against common exploits. I added it to my CloudFront distribution to block SQL injection and cross…
 Security
Security
Authentication in Web Apps: JWT, Sessions, and OAuth Explained
Authentication is one of those topics that every web developer eventually needs to understand. The two traditional approaches are session-based authenticat…
 Introduction to Claude
Introduction to Claude
Claude and Privacy: What Happens to Your Conversations?
Privacy is a legitimate concern when sharing information with any AI service, and Claude is no exception. Understanding Anthropic's data practices helps yo…
 Database
Database
PostgreSQL for Web Developers: Advanced Features You Should Know
PostgreSQL has become the database of choice for web development, but many developers only scratch the surface of its capabilities. Beyond basic SELECT que…
 Desktop Development
Desktop Development
Tauri vs Electron: Building Lightweight Desktop Apps with Web Tech
For years, Electron has been the go-to for building desktop apps with web technologies. But Tauri has emerged as a compelling alternative with fundamentall…
 Technology
Technology
Article 7 – Rights of Migrants to Pakistan
Introduction Constitution of India includes special provisions to handle the complex citizenship issues that arose after independence and partition. Artic…
 Technology
Technology
My AI Coding Workflow: From Idea to Deployed App
I have refined my AI-assisted development workflow over the past year. It starts with brainstorming where I use ChatGPT to explore architecture options. Th…
 Technology
Technology
The Privacy Trade-Off in AI Coding Assistants
Using AI coding assistants often means sharing your code with third-party servers. This privacy trade-off deserves more attention. For open-source projects…
 Technology
Technology
Avoiding Common AI Coding Pitfalls
After many mistakes, I have learned to watch for common AI coding pitfalls. Never trust generated code without understanding it, you might introduce subtle…
 Economy & Security
Economy & Security
The Red Sea Rerouting: How Houthi Attacks Are Hitting Your Indian Wallet
We often think geopolitics happens in faraway places, far away from our dinner tables. But the recent Houthi attacks on commercial vessels in the Red Sea?…
 Technology
Technology
How I Use AI for Code Review and Debugging
AI has become my first line of defense for code review and debugging. I paste problematic sections and ask for potential issues. The AI often catches edge…
 Indo-Pacific Strategy
Indo-Pacific Strategy
Understanding SAGAR: India’s Vision for the Indo-Pacific
If you’ve been following Indian foreign policy, you’ve heard the term ‘SAGAR’—Security and Growth for All in the Region. It’s meant to be India…
 Nonprofit
Nonprofit
Nonprofit and Social Impact: Doing Good for a Living
I used to work in corporate sales. I was good at it, but I felt empty. I knew I wanted my work to have more meaning. So I took a pay cut and joined a nonpr…
 Sports
Sports
Rise of T20 Cricket Leagues Around the World Global Expansion of Franchise Cricket
The rise of T20 cricket leagues has revolutionized the sport over the last two decades. The Twenty20 format, introduced in the early 2000s, shortened tradi…
 HTML/CSS/JS
HTML/CSS/JS
Form Validation: HTML5 vs JavaScript
Forms are the gateway to user data, and validating that data is crucial. You have two layers: client-side validation (for UX) and server-side validation (f…
 Human Stupidity
Human Stupidity
The Availability Heuristic: Why Rare Events Feel Common
After a plane crash receives weeks of saturation news coverage, airline ticket sales drop significantly. After a shark attack makes the front page, beach a…
 How to Use Claude
How to Use Claude
Prompt Engineering for Claude: How to Get Better Answers
The way you frame a question to Claude makes an enormous difference in the quality of the answer you get. This isn't a quirk of AI — it's actually true o…
 Security
Security
The Cyber Frontier: India’s Vulnerability to Digital Warfare
Geopolitics isn’t just about soldiers on a mountain; it’s about hackers in a basement. India has faced massive cyber attacks—the 2018 UIDAI breach, t…
 Aerospace
Aerospace
Aerospace and Defense: Reaching for the Stars
Growing up in Florida, I always watched rockets launch from Cape Canaveral. I never thought I’d be part of that world. But after getting an associate deg…
 Middle East Policy
Middle East Policy
Israel-Hamas War: India’s Delicate Balancing Walk
The conflict in Gaza put India in a tight spot. Historically, India was a staunch supporter of the Palestinian cause. But over the last decade, relations w…
 Construction
Construction
Construction Management: Building America
I started as a laborer on a construction site right out of high school. I worked my way up, learned the ropes, and went back to school for construction man…
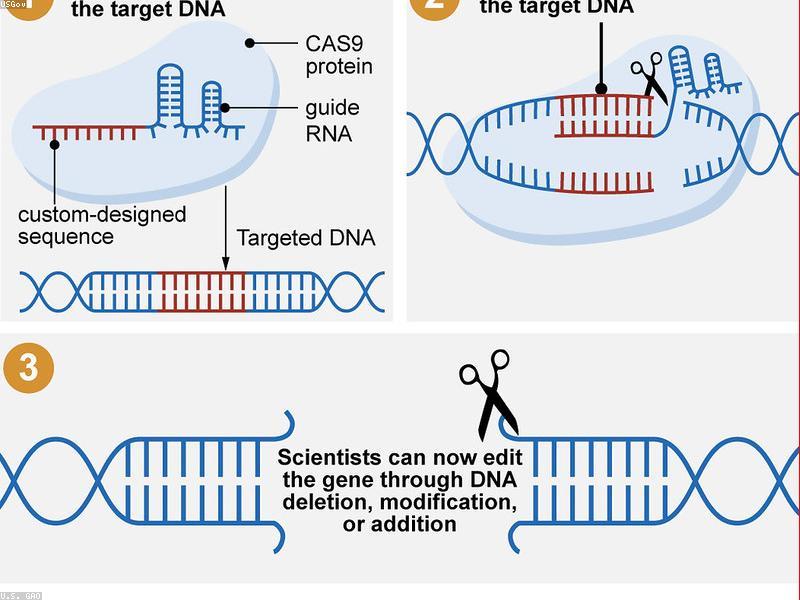 Technology
Technology
Biotechnology and CRISPR: Editing the Code of Life
CRISPR-Cas9, a groundbreaking gene-editing tool, has revolutionized biotechnology by allowing scientists to make precise changes to DNA with unprecedented…
 Google Cloud Platform
Google Cloud Platform
Running a Kubernetes Cluster for $0.10 a Day with GKE Autopilot
Kubernetes is powerful but scary. It's also expensive if you run it wrong. I had a small app that needed a database, a cache, and an API. Running this on s…
 AWS
AWS
AWS Shield: Built-in DDoS Protection
AWS Shield is a managed DDoS protection service that comes automatically with AWS. Shield Standard protects all AWS customers at no extra cost against comm…
 Technology
Technology
Edge Computing: Bringing Data Processing Closer to Home
As the volume of data generated by IoT devices explodes, cloud computing alone is no longer sufficient to handle the latency and bandwidth demands. Enter e…
 Jobs
Jobs
Tech Jobs in Dubai: Your Career in the UAE's Digital Economy
Dubai's technology sector has expanded rapidly, fuelled by government digital transformation initiatives, a growing startup ecosystem, and large corporates…
 How to Use Claude
How to Use Claude
Claude for Coding: How Developers Are Using It in Real Projects
Developers have been integrating Claude into their workflows in ways that go well beyond 'generate a function.' The ways Claude gets used in real engineeri…
 How to Use Claude
How to Use Claude
Integrating Claude with Other Tools: Workflows That Scale
Claude's value multiplies when it's integrated into existing workflows rather than used as a standalone tool you switch to separately. Here are some integr…
 History
History
The Wannsee Conference: Planning the Final Solution
January 20, 1942. Fifteen senior Nazi officials gathered in a villa on the shores of Lake Wannsee, outside Berlin. They discussed logistics, transportation…
 Technology
Technology
The Golden Age of Open Source Software
Open source software has quietly become the backbone of the modern digital economy. From the Linux operating system that powers most servers to the countle…
 Google Cloud Platform
Google Cloud Platform
Running a Kubernetes Cluster for $0.10 a Day with GKE Autopilot
Kubernetes is powerful but scary. It's also expensive if you run it wrong. I had a small app that needed a database, a cache, and an API. Running this on s…
 AWS
AWS
AWS Well-Architected Framework: Building Better
The Well-Architected Framework is a set of best practices for designing cloud systems. It covers five pillars: operational excellence, security, reliabilit…
 Maritime Security
Maritime Security
The Indian Ocean: Why Diego Garcia Keeps Strategic Planners Awake
The Indian Ocean is India’s backyard, but there are a lot of guests staying over. Diego Garcia, a tiny island in the Chagos Archipelago, hosts a massive…
 Google Cloud Platform
Google Cloud Platform
Cloud IAM: The One Thing You Must Get Right (And How I Messed It Up)
I gave a service account the 'Owner' role. I know. I'm ashamed. It was my first week on GCP. I wanted everything to just work. It did work. Too well. One d…
 Government
Government
The Public Sector: Finding Purpose in Government Work
I never thought I’d work for the government. I imagined bureaucracy and red tape. But after a layoff in the private sector, I applied for a position with…
 Foreign Policy
Foreign Policy
The I2U2 Quad: Is India Playing the West Against the East?
There’s a lot of chatter about acronyms these days—Quad, I2U2, SCO, BRICS. It can get confusing for anyone trying to keep up. I remember when the I2U2…
 Claude Comparison
Claude Comparison
Claude vs Microsoft Copilot: Which AI Tool Is Right for You?
Microsoft Copilot and Claude are targeting similar users — professionals who want AI assistance in their daily work — but they take very different appr…
 AWS
AWS
Understanding EC2: Your Virtual Server in the Cloud
Elastic Compute Cloud, or EC2, is the backbone of AWS. Think of it as renting a powerful computer online instead of buying one. You can launch a virtual se…
 Technology
Technology
Cybersecurity Threats to Watch Out for in the Coming Year
As technology evolves, so do the tactics of cybercriminals. In the coming year, experts warn of a rise in AI-powered phishing attacks that are nearly indis…
 Google Cloud Platform
Google Cloud Platform
VPC Networks: The Invisible Foundation That Saves You From Yourself
I used to ignore VPC networks. I'd just use the default network and let everything talk to everything. It was easy. It was also dangerous. One misconfigure…
 AWS
AWS
Starting Your AWS Certification Journey
AWS certifications validate your cloud knowledge and open doors. I started with the Cloud Practitioner exam, which covers foundational concepts. It's perfe…
 Technology
Technology
The Tech Stack of a Modern Startup: Tools for Success
Launching a startup today requires assembling a sophisticated technology stack that enables rapid development, efficient collaboration, and scalable growth…
 Google Cloud Platform
Google Cloud Platform
VPC Networks: The Invisible Foundation That Saves You From Yourself
I used to ignore VPC networks. I'd just use the default network and let everything talk to everything. It was easy. It was also dangerous. One misconfigure…
 Google Cloud Platform
Google Cloud Platform
Why I Finally Dumped My Old Server for Google Cloud Run (And You Should Too)
I used to be a server person. I liked having my little VPS, SSH-ing into it, installing packages manually. It felt like being a real sysadmin. But then cam…
 Google Cloud Platform
Google Cloud Platform
Why I Finally Dumped My Old Server for Google Cloud Run (And You Should Too)
I used to be a server person. I liked having my little VPS, SSH-ing into it, installing packages manually. It felt like being a real sysadmin. But then cam…
 Google Cloud Platform
Google Cloud Platform
Cloud IAM: The One Thing You Must Get Right (And How I Messed It Up)
I gave a service account the 'Owner' role. I know. I'm ashamed. It was my first week on GCP. I wanted everything to just work. It did work. Too well. One d…
 AWS
AWS
VPC Basics: Building Your Own Data Center in the Cloud
A Virtual Private Cloud is your isolated section of the AWS cloud. It's like having your own data center with complete control over networking. I found VPC…
 Technology
Technology
Robotics in the Home: From Vacuums to Companions
Robots are steadily moving out of factories and into our homes, taking on tasks that range from mundane to socially complex. The Roomba vacuum cleaner pave…
 Finance
Finance
Understanding Cryptocurrency Basics
Cryptocurrency can sound intimidating, but at its core, it’s digital money that operates on decentralized networks called blockchains. Bitcoin was the fi…
 Animals
Animals
Why Cats ‘Make Biscuits’ and What It Really Means
If you’ve ever had a cat kneading on your lap, you know the feeling of tiny claws gently pressing into you. Often called ‘making biscuits,’ this beha…
 Progressive Web Apps
Progressive Web Apps
Progressive Web Apps: Bridging Web and Native
Progressive Web Apps (PWAs) represent the best of both worlds—the reach of the web with the capabilities of native apps. A PWA is essentially a website t…
 Technology
Technology
Low-Code and No-Code Platforms: Empowering Citizen Developers
The demand for software development far exceeds the supply of skilled programmers, leading to the rise of low-code and no-code platforms. These tools allow…
 Real-Time
Real-Time
WebRTC: Building Peer-to-Peer Video and Audio Applications
WebRTC (Web Real-Time Communication) enables direct peer-to-peer audio, video, and data sharing between browsers without intermediate servers. The technolo…
 Finance
Finance
Investing 101: For Absolute Beginners
Investing can seem like a game for the wealthy, but it’s one of the most important tools for building long-term financial security. The first step is oft…
 Sci-Fi Horror
Sci-Fi Horror
Stranger Things Season 5: The Final Adventure Awaits in Hawkins
Stranger Things has become a cultural phenomenon since its debut in 2016, and the upcoming fifth season promises to be the most epic chapter yet. The Duffe…
 Technology
Technology
The Evolution of Smart Homes: Beyond Voice Assistants
Smart homes have moved far beyond simple voice commands to turn off lights. Today, the focus is on ambient intelligence—where the home anticipates your n…
 Action Thriller
Action Thriller
The Recruit Season 2: The CIA Thriller Continues
The Recruit burst onto the scene in 2022 as a fresh, energetic take on the spy thriller genre. Noah Centineo stars as Owen Hendricks, a young CIA lawyer wh…
 CMS
CMS
Headless CMS Architecture: Content Management for Modern Web
The headless CMS architecture decouples content management from content presentation, giving developers flexibility to use any frontend technology while le…
 AI Tools
AI Tools
AI-Powered Code Generation: Copilot and Beyond
AI code assistants like GitHub Copilot, Cursor, and Amazon CodeWhisperer are fundamentally changing how developers write code. These tools are trained on b…
 Thriller
Thriller
Squid Game Season 3: The Final Game Begins
Squid Game became a global phenomenon when it premiered in 2021, becoming Netflix's most-watched series of all time and sparking conversations worldwide ab…
 Personal Finance
Personal Finance
Opening Your First Bank Account in the U.S. – What Nobody Tells You
So you want to open a bank account in America. Good move. But let me tell you what the teller won't say while you're sitting there with your passport and s…
 Economy Comparison
Economy Comparison
I Lived in Both Countries for 5 Years Each – Here's What Nobody Tells You About Taxes and Savings
After living in Mumbai for five years and then Chicago for another five, I've stopped believing in easy answers about which economy is better. The US gives…
 Personal Finance
Personal Finance
Opening Your First Bank Account in the U.S. – What Nobody Tells You
So you want to open a bank account in America. Good move. But let me tell you what the teller won't say while you're sitting there with your passport and s…