 Introduction to Claude
Introduction to Claude
Claude and Privacy: What Happens to Your Conversations?
Privacy is a legitimate concern when sharing information with any AI service, and Claude is no exception. Understanding Anthropic's data practices helps yo…
Stories Worth Reading
PixelProse is your go-to blog for insightful articles on Technology, Travel, Food, Health, Lifestyle, Business, Fashion and Sports. Fresh perspectives. Real stories. Zero fluff.
Results for "information security"
145 articles found
 Introduction to Claude
Introduction to Claude
Privacy is a legitimate concern when sharing information with any AI service, and Claude is no exception. Understanding Anthropic's data practices helps yo…
 Security
Security
Content Security Policy (CSP) is one of the most effective security headers for preventing XSS attacks, yet it remains underutilized. CSP lets you define w…
 Security
Security
 Cybersecurity
Cybersecurity
I was a history major, which seems like a weird path to cybersecurity. But I was always into puzzles and logic. After taking a few online courses, I got my…
 Human Psychology
Human Psychology
You probably know someone who aced every exam, got into a top university, and still manages to make baffling choices in their personal life. Maybe that per…
 Technology
Technology
As cyber threats become more sophisticated, our defenses must evolve. AI has become an indispensable tool in the fight against cybercrime, acting as a tire…
 How to Use Claude
How to Use Claude
Enterprise adoption of Claude is growing fast, but enterprise deployments have requirements that consumer use doesn't — security, compliance, governance…
 Security
Security
Security isn't something you add after building a site—it needs to be baked into your development process. Cross-Site Scripting (XSS) remains one of the…
 Rise of America
Rise of America
In June 1947, Secretary of State George Marshall gave a commencement address at Harvard that would change the postwar world. He proposed that the United St…
 Security
Security
WebAuthn (Web Authentication) is a browser API that enables passwordless authentication using biometrics (fingerprint, face ID), security keys (YubiKey), o…
 How Claude Works
How Claude Works
You don't need to understand neural networks to use Claude well, but a basic intuition for how it generates text can help you understand why it sometimes g…
 Technology
Technology
ChatGPT is quietly transforming how people approach learning and daily work. What once required hours of searching, reading, and trial-and-error can now be…
 Introduction to Claude
Introduction to Claude
There's a version of the AI hype cycle that leads people to expect too much from Claude, and another version that leads people to dismiss it entirely. Neit…
 How Claude Works
How Claude Works
Using AI tools like Claude raises real ethical questions that thoughtful users should think through. Not all of them have clean answers, but being delibera…
 Ethics
Ethics
As AI tools become more powerful and accessible, the onus is on us, the users, to employ them responsibly. Being an ethical AI user isn't about avoiding th…
 Security
Security
Authentication is one of those topics that every web developer eventually needs to understand. The two traditional approaches are session-based authenticat…
 Rise of America
Rise of America
On the morning of September 11, 2001, the most powerful country in the world — the sole superpower of the unipolar moment, the country that had just won…
 Regional Security
Regional Security
For two decades, India invested heavily in Afghanistan—building the Parliament, roads, dams. We had a strategic partnership with the old government. Then…
 Rise of America
Rise of America
By March 4, 1933, the day Franklin Delano Roosevelt was inaugurated as the thirty-second president of the United States, the American economy was in a stat…
 Security
Security
Okay, let’s be real for a minute. Handing over your passwords and API keys to an autonomous piece of software is a security nightmare waiting to happen i…
 Lifestyle
Lifestyle
The smart home is no longer a futuristic fantasy; it's a reality, and AI is its brain. The goal of an AI-powered home is not just to have gadgets, but to c…
 Software
Software
Windows 11 requires TPM 2.0. That is a security chip. Most computers from before 2018 do not have it. Microsoft says it is for your safety. Critics say it…
 Technology
Technology
One feature that sets Grok apart is its integration with X for real-time information. When news breaks or trends emerge, Grok can access and summarize curr…
 AI Tips
AI Tips
While ChatGPT is a powerful tool, many users make simple mistakes that reduce its effectiveness. One common mistake is asking unclear or overly broad ques…
 How Claude Works
How Claude Works
Knowing when to trust Claude and when to verify is one of the most important skills for using AI tools effectively. Claude is designed to help you make thi…
 How to Use Claude
How to Use Claude
Finance professionals are finding Claude useful for a range of tasks that require combining numerical literacy with language understanding — a combinatio…
 Introduction to Claude
Introduction to Claude
Predicting the future of any technology moving as fast as AI is humbling, but looking at Anthropic's stated priorities and the trajectory of Claude's devel…
 How to Use Claude
How to Use Claude
Customer service is one of the highest-impact areas where organizations are integrating Claude. The value proposition is compelling: faster responses, more…
 How Claude Works
How Claude Works
One of the most distinctive things about Claude is its consistent emphasis on honesty — not just avoiding lies, but actively trying to give users accurat…
 Technology
Technology
Augmented Reality (AR) is poised to become a primary interface between humans and computers, overlaying digital information onto the physical world. Unlike…
 Privacy
Privacy
As AI systems become more powerful, they hunger for one thing: data. Our personal data—our searches, purchases, locations, and even our conversations—i…
 Technology
Technology
As the volume of data generated by IoT devices explodes, cloud computing alone is no longer sufficient to handle the latency and bandwidth demands. Enter e…
 Real-Time
Real-Time
WebRTC (Web Real-Time Communication) enables direct peer-to-peer audio, video, and data sharing between browsers without intermediate servers. The technolo…
 Energy Politics
Energy Politics
Energy is the currency of geopolitics. When Russia invaded Ukraine, the West expected India to jump on the sanctions bandwagon. Instead, we did the opposit…
 Technology
Technology
Remote work is here to stay, and the technology supporting it is evolving beyond simple video conferencing. The future of work is hybrid, requiring seamles…
 Jobs
Jobs
The UAE's Golden Visa programme, launched in 2019 and significantly expanded since, offers 10-year residency to a broad range of eligible individuals witho…
 Google Cloud Platform
Google Cloud Platform
We've all done it. Hardcoded API keys in config files. Committed them to Git. Then scrambled to revoke them when you realize the repo is public. I was guil…
 Google Cloud Platform
Google Cloud Platform
I used Docker Hub for a while. It was fine until I had a private image that I didn't want public. Then I discovered Artifact Registry on GCP. It's a privat…
 How to Use Claude
How to Use Claude
Beyond writing code, Claude is remarkably capable at understanding and analyzing existing codebases. For developers working in complex systems, this analys…
 Air Travel
Air Travel
I used to be the person fumbling with my shoes, holding up the line. Now, I’ve got it down to a science. Wear slip-on shoes. Have your liquids in a clear…
 Google Cloud Platform
Google Cloud Platform
We've all done it. Hardcoded API keys in config files. Committed them to Git. Then scrambled to revoke them when you realize the repo is public. I was guil…
 Google Cloud Platform
Google Cloud Platform
I used Docker Hub for a while. It was fine until I had a private image that I didn't want public. Then I discovered Artifact Registry on GCP. It's a privat…
 AWS
AWS
Key Management Service lets you create and manage encryption keys. I use it to encrypt S3 buckets, EBS volumes, and RDS databases. KMS integrates with many…
 AWS
AWS
IAM is the security guard of AWS. It controls who can access what. The biggest mistake I see beginners make is using the root user for everything. The root…
 AWS
AWS
AWS WAF is a web application firewall that helps protect against common exploits. I added it to my CloudFront distribution to block SQL injection and cross…
 Database
Database
PostgreSQL has become the database of choice for web development, but many developers only scratch the surface of its capabilities. Beyond basic SELECT que…
 Desktop Development
Desktop Development
For years, Electron has been the go-to for building desktop apps with web technologies. But Tauri has emerged as a compelling alternative with fundamentall…
 Technology
Technology
Grok entered the AI space with significant hype, largely due to its association with Elon Musk. After using it extensively, I can say it delivers on some p…
 Technology
Technology
With so many AI options, choosing can be overwhelming. Here is my practical guide. Choose Claude if you need large context windows, excellent documentation…
 Technology
Technology
Artificial Intelligence (AI) is one of the most important technological advancements of the modern world. AI refers to computer systems designed to perform…
 Technology
Technology
If you are just starting with ChatGPT, the first week can feel overwhelming. My advice is to treat it like a curious intern. Be specific in your prompts, b…
 Human Psychology
Human Psychology
Almost everyone who procrastinates believes, on some level, that the problem is laziness. That belief is wrong, and it makes procrastination worse. When yo…
 Human Psychology
Human Psychology
Edward Thorndike named the halo effect in 1920 based on his research with military officers. He noticed that officers' ratings of their soldiers were highl…
 Testing & Debugging
Testing & Debugging
Debugging is an inevitable part of programming. The better you are at it, the faster you can fix issues and move on. Python comes with a built-in debugger…
 Human Behaviour
Human Behaviour
In the 1950s, psychologist Solomon Asch ran a set of experiments so simple they almost seem like a joke. He gathered participants in a room and showed them…
 Human Psychology
Human Psychology
Here is a statistic: global child mortality has fallen by more than half since 1990, representing tens of millions of lives saved. Most people have no accu…
 Human Psychology
Human Psychology
There is a memory you have that is almost certainly wrong in at least one significant detail. You might remember a childhood event and have the location wr…
 How to Use Claude
How to Use Claude
One of Claude's most practically useful capabilities is summarizing long documents. Whether you're dealing with a lengthy research paper, a dense legal con…
 Human Psychology
Human Psychology
Someone cuts you off in traffic and you immediately form a judgment about what kind of person they are. Then, a few minutes later, you cut someone else off…
 AI
AI
Many users give vague prompts or expect perfect answers without reviewing them. Always verify information and refine your queries for better results
 AI
AI
ChatGPT is helpful but not always perfect. It may give outdated or incorrect answers, so double-check important information
 Human Stupidity
Human Stupidity
In 1961, a group of some of the most intelligent, educated, and experienced people in the United States government met repeatedly to plan the Bay of Pigs i…
 Human Psychology
Human Psychology
Before you answer the next question, spin an imaginary wheel of fortune. It stops on 65. Now: what percentage of African countries are members of the Unite…
 Jobs
Jobs
Dubai has not stopped building since the 1970s and shows no sign of stopping now. The city's infrastructure pipeline includes new metro extensions, megapro…
 Human Resources
Human Resources
I fell into Human Resources by accident. I was an administrative assistant, and the HR manager asked if I wanted to help with recruitment. I found that I l…
 How to Use Claude
How to Use Claude
Building a functional chatbot with Claude is more achievable than most people expect, even with modest programming experience. Here's a practical starting…
 Core Concepts
Core Concepts
Variables are like labeled boxes where you store information. In Python, you don't need to declare what type of data a variable will hold. You simply assig…
 Introduction to Claude
Introduction to Claude
Claude has evolved significantly since its initial release. Looking at the arc of development gives useful context for what the model can do now and where…
 AI
AI
Unlike search engines, ChatGPT gives direct answers instead of links. However, it may not always provide updated information
 How Claude Works
How Claude Works
The ability to reason through complex, multi-step problems is what separates truly useful AI from simple text generators. Claude's reasoning capabilities a…
 How Claude Works
How Claude Works
One of the technical features that comes up often in discussions about Claude is its context window. If you've ever had an AI assistant forget what you wer…
 AI
AI
ChatGPT is generally safe, but users should avoid sharing personal or sensitive information. Always use it responsibly
 Technology
Technology
Social media platforms are meticulously designed to capture and hold our attention, but the psychological impact of these algorithms is profound. These sys…
 Technology
Technology
You've heard of ChatGPT, but how does it actually work? Under the hood, it's powered by a Large Language Model, or LLM. At its core, an LLM is a type of ar…
 How Claude Works
How Claude Works
What did Claude read to become what it is? The training data for large language models is one of the least transparent aspects of AI development, but what'…
 How to Use Claude
How to Use Claude
Healthcare organizations are exploring Claude carefully, with appropriate caution about where AI assistance is safe and valuable versus where it requires h…
 AI Tips
AI Tips
Even though Claude 5 is powerful, many users do not get the best results because of simple mistakes. One major issue is giving unclear instructions. When…
 Google Cloud Platform
Google Cloud Platform
I've used all the major clouds. AWS's console feels like a government website from 2005. Azure's feels like a maze where every hallway looks the same. But…
 Healthcare
Healthcare
ChatGPT can assist with information and documentation but cannot replace medical professionals
 How Claude Works
How Claude Works
When you type a message to Claude, a lot happens before you see a response. Understanding the basics of how Claude works can help you use it more effective…
 How to Use Claude
How to Use Claude
The people who get the most out of Claude aren't necessarily the ones doing the most impressive things. Often it's the people who've figured out simple, re…
 Google Cloud Platform
Google Cloud Platform
I've used all the major clouds. AWS's console feels like a government website from 2005. Azure's feels like a maze where every hallway looks the same. But…
 Career
Career
The conversation around AI and jobs often focuses on automation and displacement, but a more nuanced view reveals a future where AI acts as a powerful coll…
 Stack Overflow
Stack Overflow
Getting your first downvote on Stack Overflow stings. It feels personal, like someone said your baby is ugly. My first one was on a question I’d spent ho…
 AI Basics
AI Basics
Artificial Intelligence. It sounds like something from a sci-fi movie, doesn't it? The truth is, AI is already woven into the fabric of our daily lives, fr…
 Ethics
Ethics
With great power comes great responsibility. As AI becomes more integrated into our lives, it’s crucial to have an honest conversation about its ethical…
 HTML
HTML
If you're building websites in 2024, you've probably heard about semantic HTML, but do you really understand why it's so important? Semantic elements like…
 Education
Education
Filling the UPSC Civil Services Exam form is the first real test. Not of your knowledge, but of your patience. The form looks simple, but one wrong entry c…
 UPSC Mains Strategy
UPSC Mains Strategy
Let me be honest with you. Most UPSC aspirants clear Prelims but fail Mains. Why? Because Prelims is about choosing the right option. Mains is about writin…
 Technology
Technology
Introduction Constitution of India includes special provisions to handle the complex citizenship issues that arose after independence and partition. Artic…
 Technology
Technology
I have refined my AI-assisted development workflow over the past year. It starts with brainstorming where I use ChatGPT to explore architecture options. Th…
 Technology
Technology
Using AI coding assistants often means sharing your code with third-party servers. This privacy trade-off deserves more attention. For open-source projects…
 Technology
Technology
After many mistakes, I have learned to watch for common AI coding pitfalls. Never trust generated code without understanding it, you might introduce subtle…
 Economy & Security
Economy & Security
We often think geopolitics happens in faraway places, far away from our dinner tables. But the recent Houthi attacks on commercial vessels in the Red Sea?…
 Technology
Technology
AI has become my first line of defense for code review and debugging. I paste problematic sections and ask for potential issues. The AI often catches edge…
 Indo-Pacific Strategy
Indo-Pacific Strategy
If you’ve been following Indian foreign policy, you’ve heard the term ‘SAGAR’—Security and Growth for All in the Region. It’s meant to be India…
 Nonprofit
Nonprofit
I used to work in corporate sales. I was good at it, but I felt empty. I knew I wanted my work to have more meaning. So I took a pay cut and joined a nonpr…
 Sports
Sports
The rise of T20 cricket leagues has revolutionized the sport over the last two decades. The Twenty20 format, introduced in the early 2000s, shortened tradi…
 HTML/CSS/JS
HTML/CSS/JS
Forms are the gateway to user data, and validating that data is crucial. You have two layers: client-side validation (for UX) and server-side validation (f…
 Human Stupidity
Human Stupidity
After a plane crash receives weeks of saturation news coverage, airline ticket sales drop significantly. After a shark attack makes the front page, beach a…
 How to Use Claude
How to Use Claude
The way you frame a question to Claude makes an enormous difference in the quality of the answer you get. This isn't a quirk of AI — it's actually true o…
 Security
Security
Geopolitics isn’t just about soldiers on a mountain; it’s about hackers in a basement. India has faced massive cyber attacks—the 2018 UIDAI breach, t…
 Aerospace
Aerospace
Growing up in Florida, I always watched rockets launch from Cape Canaveral. I never thought I’d be part of that world. But after getting an associate deg…
 Middle East Policy
Middle East Policy
The conflict in Gaza put India in a tight spot. Historically, India was a staunch supporter of the Palestinian cause. But over the last decade, relations w…
 Construction
Construction
I started as a laborer on a construction site right out of high school. I worked my way up, learned the ropes, and went back to school for construction man…
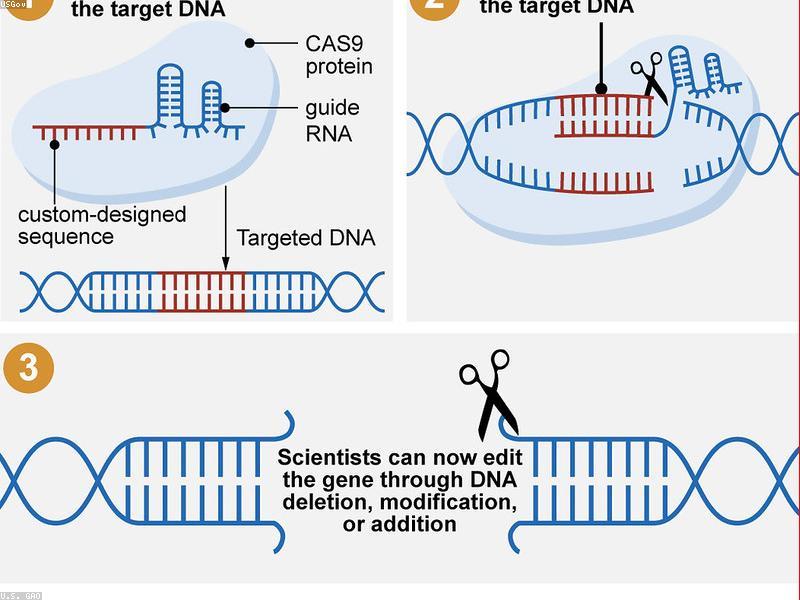 Technology
Technology
CRISPR-Cas9, a groundbreaking gene-editing tool, has revolutionized biotechnology by allowing scientists to make precise changes to DNA with unprecedented…
 Google Cloud Platform
Google Cloud Platform
Kubernetes is powerful but scary. It's also expensive if you run it wrong. I had a small app that needed a database, a cache, and an API. Running this on s…
 AWS
AWS
AWS Shield is a managed DDoS protection service that comes automatically with AWS. Shield Standard protects all AWS customers at no extra cost against comm…
 Jobs
Jobs
Dubai's technology sector has expanded rapidly, fuelled by government digital transformation initiatives, a growing startup ecosystem, and large corporates…
 How to Use Claude
How to Use Claude
Developers have been integrating Claude into their workflows in ways that go well beyond 'generate a function.' The ways Claude gets used in real engineeri…
 How to Use Claude
How to Use Claude
Claude's value multiplies when it's integrated into existing workflows rather than used as a standalone tool you switch to separately. Here are some integr…
 History
History
January 20, 1942. Fifteen senior Nazi officials gathered in a villa on the shores of Lake Wannsee, outside Berlin. They discussed logistics, transportation…
 Technology
Technology
Open source software has quietly become the backbone of the modern digital economy. From the Linux operating system that powers most servers to the countle…
 Google Cloud Platform
Google Cloud Platform
Kubernetes is powerful but scary. It's also expensive if you run it wrong. I had a small app that needed a database, a cache, and an API. Running this on s…
 AWS
AWS
The Well-Architected Framework is a set of best practices for designing cloud systems. It covers five pillars: operational excellence, security, reliabilit…
 Maritime Security
Maritime Security
The Indian Ocean is India’s backyard, but there are a lot of guests staying over. Diego Garcia, a tiny island in the Chagos Archipelago, hosts a massive…
 Google Cloud Platform
Google Cloud Platform
I gave a service account the 'Owner' role. I know. I'm ashamed. It was my first week on GCP. I wanted everything to just work. It did work. Too well. One d…
 Government
Government
I never thought I’d work for the government. I imagined bureaucracy and red tape. But after a layoff in the private sector, I applied for a position with…
 Foreign Policy
Foreign Policy
There’s a lot of chatter about acronyms these days—Quad, I2U2, SCO, BRICS. It can get confusing for anyone trying to keep up. I remember when the I2U2…
 Claude Comparison
Claude Comparison
Microsoft Copilot and Claude are targeting similar users — professionals who want AI assistance in their daily work — but they take very different appr…
 AWS
AWS
Elastic Compute Cloud, or EC2, is the backbone of AWS. Think of it as renting a powerful computer online instead of buying one. You can launch a virtual se…
 Technology
Technology
As technology evolves, so do the tactics of cybercriminals. In the coming year, experts warn of a rise in AI-powered phishing attacks that are nearly indis…
 Google Cloud Platform
Google Cloud Platform
I used to ignore VPC networks. I'd just use the default network and let everything talk to everything. It was easy. It was also dangerous. One misconfigure…
 AWS
AWS
AWS certifications validate your cloud knowledge and open doors. I started with the Cloud Practitioner exam, which covers foundational concepts. It's perfe…
 Technology
Technology
Launching a startup today requires assembling a sophisticated technology stack that enables rapid development, efficient collaboration, and scalable growth…
 Google Cloud Platform
Google Cloud Platform
I used to ignore VPC networks. I'd just use the default network and let everything talk to everything. It was easy. It was also dangerous. One misconfigure…
 Google Cloud Platform
Google Cloud Platform
I used to be a server person. I liked having my little VPS, SSH-ing into it, installing packages manually. It felt like being a real sysadmin. But then cam…
 Google Cloud Platform
Google Cloud Platform
I used to be a server person. I liked having my little VPS, SSH-ing into it, installing packages manually. It felt like being a real sysadmin. But then cam…
 Google Cloud Platform
Google Cloud Platform
I gave a service account the 'Owner' role. I know. I'm ashamed. It was my first week on GCP. I wanted everything to just work. It did work. Too well. One d…
 AWS
AWS
A Virtual Private Cloud is your isolated section of the AWS cloud. It's like having your own data center with complete control over networking. I found VPC…
 Technology
Technology
Robots are steadily moving out of factories and into our homes, taking on tasks that range from mundane to socially complex. The Roomba vacuum cleaner pave…
 Finance
Finance
Cryptocurrency can sound intimidating, but at its core, it’s digital money that operates on decentralized networks called blockchains. Bitcoin was the fi…
 Animals
Animals
If you’ve ever had a cat kneading on your lap, you know the feeling of tiny claws gently pressing into you. Often called ‘making biscuits,’ this beha…
 Progressive Web Apps
Progressive Web Apps
Progressive Web Apps (PWAs) represent the best of both worlds—the reach of the web with the capabilities of native apps. A PWA is essentially a website t…
 Technology
Technology
The demand for software development far exceeds the supply of skilled programmers, leading to the rise of low-code and no-code platforms. These tools allow…
 Finance
Finance
Investing can seem like a game for the wealthy, but it’s one of the most important tools for building long-term financial security. The first step is oft…
 Sci-Fi Horror
Sci-Fi Horror
Stranger Things has become a cultural phenomenon since its debut in 2016, and the upcoming fifth season promises to be the most epic chapter yet. The Duffe…
 Technology
Technology
Smart homes have moved far beyond simple voice commands to turn off lights. Today, the focus is on ambient intelligence—where the home anticipates your n…
 Action Thriller
Action Thriller
The Recruit burst onto the scene in 2022 as a fresh, energetic take on the spy thriller genre. Noah Centineo stars as Owen Hendricks, a young CIA lawyer wh…
 CMS
CMS
The headless CMS architecture decouples content management from content presentation, giving developers flexibility to use any frontend technology while le…
 AI Tools
AI Tools
AI code assistants like GitHub Copilot, Cursor, and Amazon CodeWhisperer are fundamentally changing how developers write code. These tools are trained on b…
 Thriller
Thriller
Squid Game became a global phenomenon when it premiered in 2021, becoming Netflix's most-watched series of all time and sparking conversations worldwide ab…
 Personal Finance
Personal Finance
So you want to open a bank account in America. Good move. But let me tell you what the teller won't say while you're sitting there with your passport and s…
 Economy Comparison
Economy Comparison
After living in Mumbai for five years and then Chicago for another five, I've stopped believing in easy answers about which economy is better. The US gives…
 Personal Finance
Personal Finance
So you want to open a bank account in America. Good move. But let me tell you what the teller won't say while you're sitting there with your passport and s…